System infographic
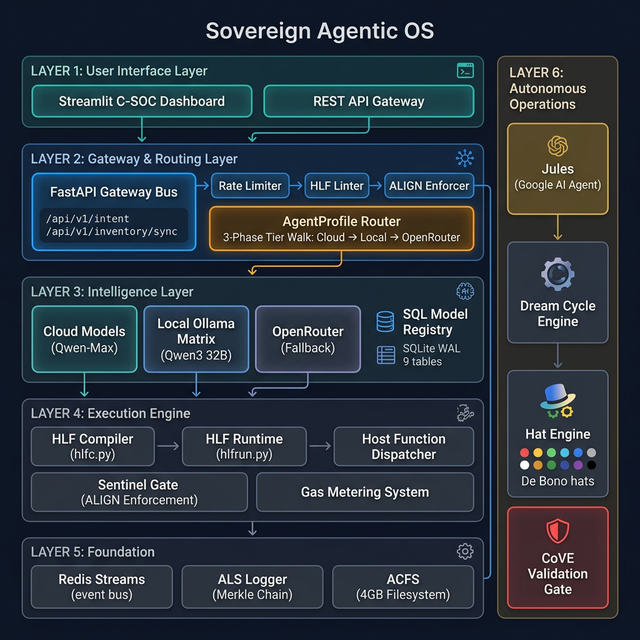
A single-screen briefing for the repo’s layered architecture: ACFS confinement at the base, HLF logic and governance in the middle, and observability plus memory on the upper tiers.
Open source SVG →Watch natural language transform into deterministic hieroglyphic instructions, get processed by agents, and translate back — with live metrics.
This visual layer distills the full repository scan into an at-a-glance briefing: what the major layers are, how an intent moves through them, and where governance, memory, and runtime boundaries show up in the stack.
A single-screen briefing for the repo’s layered architecture: ACFS confinement at the base, HLF logic and governance in the middle, and observability plus memory on the upper tiers.
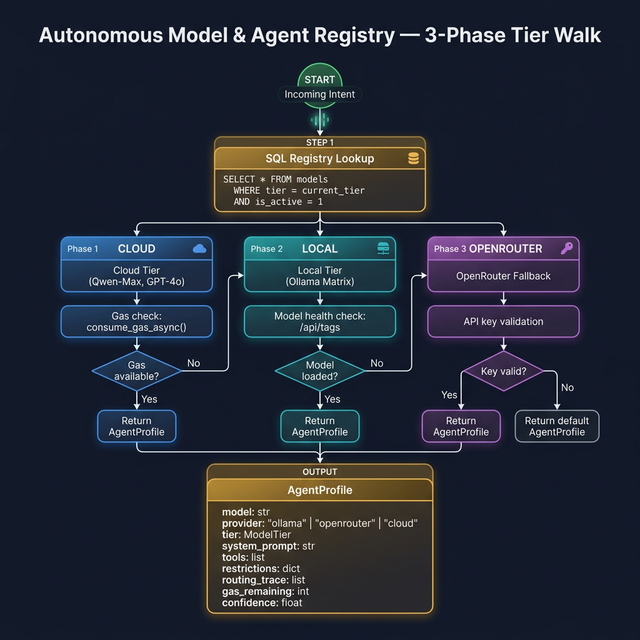
Open source SVG →Four slide-style summaries map the major discovery passes: overview, architecture, flow analysis, and deep-dive surfaces that are easy to miss on a first read.
A cinematic strip for the live demo: authored intent, compiler pass, governance envelope, then audit + memory persistence. It turns the stack’s control flow into something a reader can absorb in seconds.
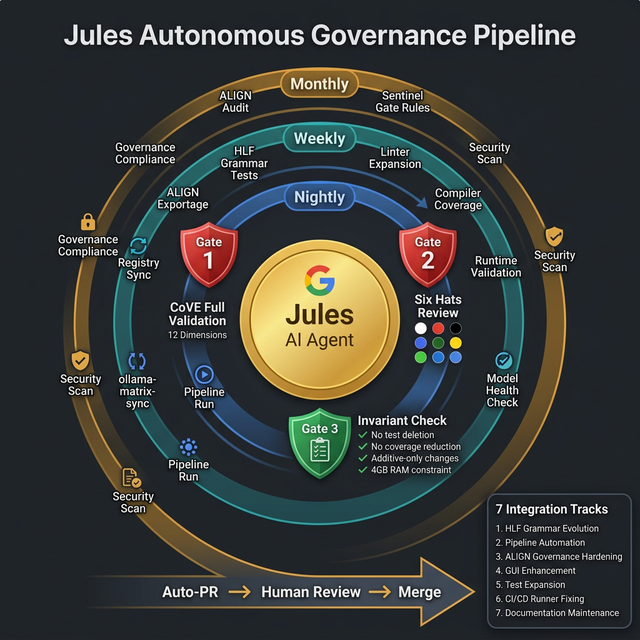
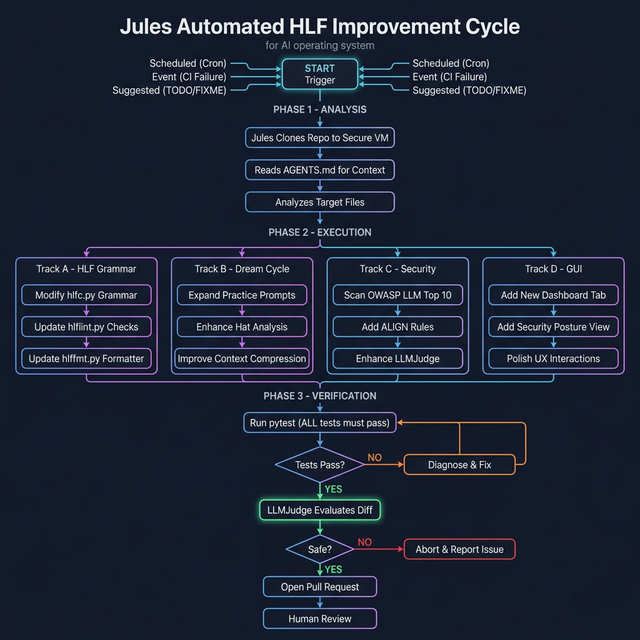
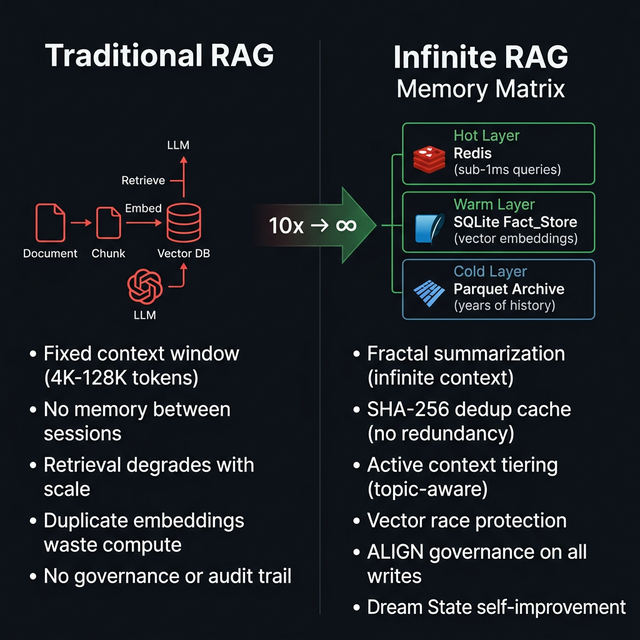
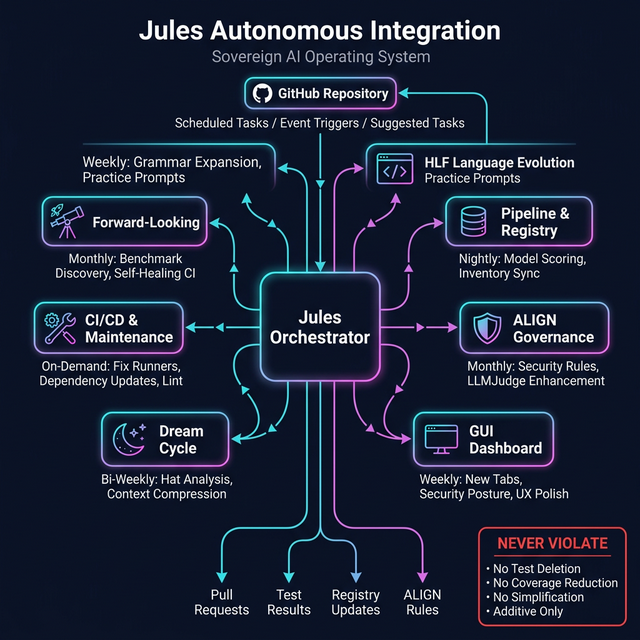
Open source SVG →I reviewed the older media set and brought back the pieces that still do the most work for readers: architecture, routing, governance, Jules orchestration, and the Infinite RAG comparison.
This live demo limits translations to 5 per day to conserve shared resources. Fork the repo and deploy your own instance for unlimited translations, your own Jules agent swarm, and the ability to contribute HLF grammar evolutions back to the canonical spec.
Each fork running its own agent swarm contributes to exponential language improvement. Your agents propose grammar evolutions (RFC 9006), which get validated and merged upstream, making HLF better for everyone — for programming, product creation, and multi-agent orchestration.
gh repo fork Grumpified-OGGVCT/Sovereign_Agentic_OS_with_HLF --clone cd Sovereign_Agentic_OS_with_HLF uv sync
Copy the template and fill in your credentials:
cp .env.example .env
Required keys in your .env file:
REDIS_PASSWORD — Redis auth (for gateway message bus)OPENROUTER_API_KEY — Cloud model access (Sovereign tier)GITHUB_TOKEN — For Copilot factory / agent dispatchOptional but recommended:
OLLAMA_HOST — Primary Ollama endpoint (default: http://localhost:11434)OLLAMA_HOST_SECONDARY — Secondary Ollama at :11435 (doubles cloud quota)OLLAMA_LOAD_STRATEGY — failover | round_robin | primary_onlySLACK_WEBHOOK_URL — Agent alert notificationsSTREAMLIT_SECRET_KEY — GUI session encryption⚠️ Never commit your .env file — it's already gitignored with 70+ rules.
Save all keys in .env at the project root. The system auto-loads them via python-dotenv.
Jules is your autonomous maintenance & evolution agent. To set up your own upgraded swarm:
config/jules_tasks.yamlWith your own swarm, you get:
# Enable GitHub Pages (Settings → Pages → Source: GitHub Actions → Static HTML) # Set path to ./docs # Your translations are now unlimited — no quota on self-hosted forks!
# List available agent task templates python scripts/copilot_factory.py list-templates # Dispatch an HLF test agent (dry run first) python scripts/copilot_factory.py hlf-test --dry-run # Create a live Copilot agent issue python scripts/copilot_factory.py hlf-evolve
Read the full HLF specification and architecture docs in the repo:
source_knowlwedge/HLF_The_Hieroglyphic_Logic_Framework_for_Agentic_Orchestration.mdsource_knowlwedge/RFC_9005_The_HLF_Native_Language_Specification_v3.0.mdsource_knowlwedge/The_HLF_v3.0_Protocol_Transparent_Compression_in_Systems_Programming.mdbuild_notes/HLF_Core_A_Sovereign_Architecture_for_Secure_Agentic_OS.mdAGENTS.md — Security invariants and test conventions